Introduction
Students gain an understanding of the impact of architectural and network security for enterprises. This course prepares students with the ability to recognize threats to modern networks and select appropriate security tools to safeguard them. New challenges associated with securing new types of networks, including cloud configurations and the Internet of Things, and provide guidance on evaluating their complexities are also explored.
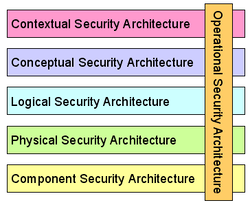
Security Architecture Artifacts & The SABSA Architecture
Security architecture artifacts, such as diagrams, models, and documentation, are valuable tools for maintaining consistency and traceability in security design because they provide a visual and documented representation of the security design. These artifacts help ensure that the security design is consistent with the organization's security policies, standards, and best practices. They also provide a record of the decision-making process behind the security design, including the rationale for specific security controls, their placement, and their interactions with other controls. In this way, security architecture artifacts help maintain traceability and accountability in the security design process, making it easier to identify and address any issues that may arise during implementation or future audits. The SABSA architecture is a widely recognized security architecture framework that consists of seven layers. The five main layers of the SABSA architecture are the Contextual, Conceptual, Logical, Physical, and Component layers. These layers are interdependent and interrelated, with each layer building upon the previous one to form a comprehensive security architecture. The Contextual layer provides the foundation for the SABSA architecture by establishing the context and scope for the security design. The Conceptual layer builds upon this foundation by defining the business requirements, security objectives, and risk management strategies. The Logical layer then translates the conceptual requirements into a high-level security design that outlines the security services, security domains, and security components necessary to meet the security objectives. The Physical layer then takes the logical design and maps it onto the physical infrastructure, taking into account the technical and operational constraints of the environment. Finally, the Component layer defines the specific security components, such as firewalls, intrusion detection systems, and authentication systems, that make up the overall security architecture. By understanding the relationship between these five main layers of the SABSA architecture, security architects can develop a comprehensive and cohesive security design that is aligned with business objectives, compliant with regulatory requirements, and resilient to security threats. The SABSA architecture provides a structured and systematic approach to security design that enables organizations to create a robust security architecture that meets their specific needs and requirements.
Deep-Dive into SABSA Architecture
The Contextual layer
The Contextual layer is a component of the SABSA Architecture that provides the foundation for the security design. This layer defines the context and scope of the security architecture and establishes the business drivers, governance requirements, and risk management strategies that will inform the security design. The Contextual layer helps ensure that the security design is aligned with the business objectives and requirements of the organization. By defining the context and scope of the security architecture, the Contextual layer helps security architects identify the specific risks and threats that need to be addressed and develop a security design that is tailored to the needs of the organization. the Contextual layer helps establish the governance requirements and compliance obligations that must be met, such as regulatory requirements or industry standards. By considering these requirements from the outset, security architects can ensure that the security design is compliant with all relevant regulations and standards, reducing the risk of costly and time-consuming remediation efforts later on.
The Conceptual layer
The Conceptual layer of the SABSA model is critical because it provides a foundation for developing an effective security architecture that is closely aligned with the organization's business objectives and risk management strategy. This layer emphasizes the importance of understanding the organization's business context, objectives, and strategies, as well as the risks and compliance requirements that need to be addressed. By defining these key factors at the Conceptual layer, security professionals can develop a security strategy and architecture that is well-aligned with the organization's overall goals and objectives, and that addresses the most critical risks and compliance requirements.
The Logical layer
The Logical layer emphasizes the importance of defining the logical relationships and dependencies between different security services and components, as well as the interfaces and protocols that will be used to integrate them into a cohesive security solution. By defining the logical architecture at this layer, security professionals can ensure that the security services and components are well-designed, efficient, and effective, and that they can be easily integrated and managed within the organization's existing technology and infrastructure.
The Physical layer
This layer emphasizes the importance of selecting and configuring the appropriate physical technology and infrastructure to support the security components and services and ensuring that they are integrated and managed effectively within the organization's overall technology infrastructure. By defining the Physical layer, security professionals can ensure that the security solution is not only well-designed and efficient but also that it is physically secure and resilient. Without a well-defined Physical layer, the security architecture may not be able to effectively protect the organization's assets and data against physical threats such as theft, vandalism, or natural disasters. A poorly designed Physical layer may result in operational inefficiencies, higher costs, and a greater risk of system failures.
The Component layer
The Component layer emphasizes the importance of selecting and configuring the appropriate security technologies and infrastructure to support the security services. By defining the Component layer, security professionals can ensure that the security components are well-designed, properly integrated, and configured to support the overall security architecture and services. This layer also helps to identify any gaps or overlaps in the security technology and infrastructure and helps to ensure that the organization is using the most effective and efficient security solutions available. Without a well-defined Component layer, security solutions may not be properly integrated or may not adequately address the organization's security requirements, which can result in security breaches or operational inefficiencies.
The Contextual layer is a component of the SABSA Architecture that provides the foundation for the security design. This layer defines the context and scope of the security architecture and establishes the business drivers, governance requirements, and risk management strategies that will inform the security design. The Contextual layer helps ensure that the security design is aligned with the business objectives and requirements of the organization. By defining the context and scope of the security architecture, the Contextual layer helps security architects identify the specific risks and threats that need to be addressed and develop a security design that is tailored to the needs of the organization. the Contextual layer helps establish the governance requirements and compliance obligations that must be met, such as regulatory requirements or industry standards. By considering these requirements from the outset, security architects can ensure that the security design is compliant with all relevant regulations and standards, reducing the risk of costly and time-consuming remediation efforts later on.
The Conceptual layer
The Conceptual layer of the SABSA model is critical because it provides a foundation for developing an effective security architecture that is closely aligned with the organization's business objectives and risk management strategy. This layer emphasizes the importance of understanding the organization's business context, objectives, and strategies, as well as the risks and compliance requirements that need to be addressed. By defining these key factors at the Conceptual layer, security professionals can develop a security strategy and architecture that is well-aligned with the organization's overall goals and objectives, and that addresses the most critical risks and compliance requirements.
The Logical layer
The Logical layer emphasizes the importance of defining the logical relationships and dependencies between different security services and components, as well as the interfaces and protocols that will be used to integrate them into a cohesive security solution. By defining the logical architecture at this layer, security professionals can ensure that the security services and components are well-designed, efficient, and effective, and that they can be easily integrated and managed within the organization's existing technology and infrastructure.
The Physical layer
This layer emphasizes the importance of selecting and configuring the appropriate physical technology and infrastructure to support the security components and services and ensuring that they are integrated and managed effectively within the organization's overall technology infrastructure. By defining the Physical layer, security professionals can ensure that the security solution is not only well-designed and efficient but also that it is physically secure and resilient. Without a well-defined Physical layer, the security architecture may not be able to effectively protect the organization's assets and data against physical threats such as theft, vandalism, or natural disasters. A poorly designed Physical layer may result in operational inefficiencies, higher costs, and a greater risk of system failures.
The Component layer
The Component layer emphasizes the importance of selecting and configuring the appropriate security technologies and infrastructure to support the security services. By defining the Component layer, security professionals can ensure that the security components are well-designed, properly integrated, and configured to support the overall security architecture and services. This layer also helps to identify any gaps or overlaps in the security technology and infrastructure and helps to ensure that the organization is using the most effective and efficient security solutions available. Without a well-defined Component layer, security solutions may not be properly integrated or may not adequately address the organization's security requirements, which can result in security breaches or operational inefficiencies.
Reflection
In today's highly connected and technology-driven world, the security of enterprise networks and systems is of utmost importance. With the increasing sophistication of cyber threats, it has become critical for organizations to adopt a proactive approach towards security architecture and network security. This course is designed to provide students with an in-depth understanding of the importance of security architecture and network security at the enterprise level. Using security architecture frameworks, in this class we explored enterprise security architectures and learned to identify appropriate security tools to safeguard networks. The course covered the evaluation of the complexities of securing new types of networks, such as cloud configurations and the Internet of Things. By the end of the course, I was equipped with the knowledge and skills necessary to address the ever-evolving challenges in enterprise security and make informed decisions to mitigate risks and protect their organization's sensitive data and assets. In this course on architectural and network security at the enterprise level is crucial for professionals who want to establish and maintain a secure network infrastructure in their organization. In this course, I wanted to learn about the different types of security threats that exist in today's networks and how to identify appropriate security tools to safeguard against them. I desired to gain an understanding of security architecture frameworks and how to use them to design and implement effective security measures. Moreover, I anticipated that this course would cover the complexities involved in securing new types of networks, such as cloud configurations and the Internet of Things. By the end of the course, I expected to have a comprehensive understanding of enterprise security and be able to evaluate and implement security measures that are specific to my organization's needs.
The most interesting topic of study was the SABSA framework which provides several valuable lessons for security professionals to apply toward organizational security. It highlights the importance of taking a risk-based approach to security and aligning security solutions with an organization's overall business objectives. It emphasizes the importance of understanding the organization's business context, risk appetite, and compliance requirements, and developing a well-defined security strategy and architecture that addresses the most critical risks. The framework also highlights the importance of taking a holistic and integrated approach to security architecture, and the need to define well-measured and measurable security services and components. The SABSA framework provides a structured approach to implementing security solutions, with a focus on having a well-defined implementation plan that considers the organization's existing technology and infrastructure. By studying the SABSA framework, security professionals and organizations can develop effective security architectures that provide reliable and comprehensive protection against a wide range of security threats.
By studying the SABSA framework, security professionals and organizations can develop effective security architectures that provide reliable and comprehensive protection against a wide range of security threats. As a cloud professional I have been able to apply the SABSA framework to the cloud to develop and implement effective security architectures that are tailored to customers specific cloud environments. The framework helps to identify the unique risks and challenges associated with cloud computing, and to develop a well-defined security strategy and architecture that addresses these risks. In the Business Context layer, organizations can analyze the business objectives and risks associated with the use of cloud computing and develop a cloud-specific risk management strategy. The Strategy layer can become focused on defining cloud-specific security policies and guidelines that align with the organization's overall security strategy. The Security Architecture layer can define the security services and components that are required to support the cloud environment, considering the unique characteristics of cloud computing such as elasticity, scalability, and virtualization. The Security Services layer can focus on defining well-measured and measurable security services that are specific to the cloud environment, such as identity and access management, network security, and data protection. The Component layer can focus on selecting and configuring cloud-specific security technologies and infrastructure, such as encryption, firewalls, and intrusion detection systems. Finally, the Implementation layer can focus on implementing the cloud-specific security components and services. Applying the SABSA framework to the cloud can help organizations to develop comprehensive and effective security architectures that are well-aligned with their business objectives and specific cloud environments. Learning these strategies has helped me to become a better cloud professional.
In conclusion, the importance of security architecture and network security at the enterprise level cannot be overstated in today's world of increasing cyber threats. Through this course, I gained an in-depth understanding of security architecture frameworks and how to identify appropriate security tools to safeguard networks. The SABSA framework provided valuable lessons for developing and implementing effective security architectures that are aligned with business objectives. Applying this framework to the cloud environment can help organizations to address the unique risks and challenges associated with cloud computing and develop comprehensive and effective security architectures. This course equipped me with the knowledge and skills necessary to make informed decisions to mitigate risks and protect my organization's sensitive data and assets. As a cloud professional, I am now better equipped to design and implement effective security measures that are specific to my customers' needs, ultimately helping to ensure the security and integrity of their cloud environments.
The most interesting topic of study was the SABSA framework which provides several valuable lessons for security professionals to apply toward organizational security. It highlights the importance of taking a risk-based approach to security and aligning security solutions with an organization's overall business objectives. It emphasizes the importance of understanding the organization's business context, risk appetite, and compliance requirements, and developing a well-defined security strategy and architecture that addresses the most critical risks. The framework also highlights the importance of taking a holistic and integrated approach to security architecture, and the need to define well-measured and measurable security services and components. The SABSA framework provides a structured approach to implementing security solutions, with a focus on having a well-defined implementation plan that considers the organization's existing technology and infrastructure. By studying the SABSA framework, security professionals and organizations can develop effective security architectures that provide reliable and comprehensive protection against a wide range of security threats.
By studying the SABSA framework, security professionals and organizations can develop effective security architectures that provide reliable and comprehensive protection against a wide range of security threats. As a cloud professional I have been able to apply the SABSA framework to the cloud to develop and implement effective security architectures that are tailored to customers specific cloud environments. The framework helps to identify the unique risks and challenges associated with cloud computing, and to develop a well-defined security strategy and architecture that addresses these risks. In the Business Context layer, organizations can analyze the business objectives and risks associated with the use of cloud computing and develop a cloud-specific risk management strategy. The Strategy layer can become focused on defining cloud-specific security policies and guidelines that align with the organization's overall security strategy. The Security Architecture layer can define the security services and components that are required to support the cloud environment, considering the unique characteristics of cloud computing such as elasticity, scalability, and virtualization. The Security Services layer can focus on defining well-measured and measurable security services that are specific to the cloud environment, such as identity and access management, network security, and data protection. The Component layer can focus on selecting and configuring cloud-specific security technologies and infrastructure, such as encryption, firewalls, and intrusion detection systems. Finally, the Implementation layer can focus on implementing the cloud-specific security components and services. Applying the SABSA framework to the cloud can help organizations to develop comprehensive and effective security architectures that are well-aligned with their business objectives and specific cloud environments. Learning these strategies has helped me to become a better cloud professional.
In conclusion, the importance of security architecture and network security at the enterprise level cannot be overstated in today's world of increasing cyber threats. Through this course, I gained an in-depth understanding of security architecture frameworks and how to identify appropriate security tools to safeguard networks. The SABSA framework provided valuable lessons for developing and implementing effective security architectures that are aligned with business objectives. Applying this framework to the cloud environment can help organizations to address the unique risks and challenges associated with cloud computing and develop comprehensive and effective security architectures. This course equipped me with the knowledge and skills necessary to make informed decisions to mitigate risks and protect my organization's sensitive data and assets. As a cloud professional, I am now better equipped to design and implement effective security measures that are specific to my customers' needs, ultimately helping to ensure the security and integrity of their cloud environments.

